
- 2020 | CommerceBasix Contact Us 0


You can’t visit a Starbucks today and not see at least one person using Wi-Fi to connect their smartphone or laptop to the Internet. Believe it or not, it wasn’t always that way. In fact, a firm that Mark co-founded, [MobileStar], convinced Howard Schultz and his staff in December 2000 to let MobileStar be the exclusive Wi-Fi provider for Starbucks.
When Mark and his co-founder began their new venture in 1996, the Internet was in its infancy and Starbucks was just beginning its national expansion. But there was an interesting intersection that Mark and his team believed would happen in the near future: business travelers who made frequent use of their corporate networks, synchronized Notes databases, downloaded large PowerPoint files, and used email (yes, it was still rather new) would want to do that more quickly than they could with a telephone dial-up connection (28.8 kbps). And they would love to do that without a wired connection. It was an idea that sounded like science fiction at the time.
This idea was, to use a popular phrase these days, a Big Hairy Audacious Goal. Why? First, the IEEE committee standardizing what would become Wi-Fi hadn’t finished finalizing that standard yet. Second, the only way to get a Wi-Fi radio for your laptop was to purchase one as an optional add-on; it wasn’t built in. Third, most investors believed that 3G or the soon-to-be-launched Iridium satellite network would fill this need. Fourth, no one believed that a startup, a new venture, could possibly build out this kind of national network.
It turns out, these well intentioned and well educated investors and advisors were all wrong. And the MobileStar team was right.
After raising $65M in capital and $20M in debt, Mark and his team had secured exclusive Wi-Fi network deployment agreements with Hilton Hotels and American Airlines. And in December 2000, Mark met with Howard Schulz in his office to sign Starbucks as its next “footprint customer.”
The conversation went like this:
Howard: “So, you’re telling me that if I let you install this wireless network in my coffee shops, people might spend an extra five minutes downloading their email and might buy another latte. Do I have that right?”
Mark: “Yes. That is what our research shows.”
Howard: “Well, since you’re paying for the network, we’ll do this and see if your research proves correct.”
And Howard signed the exclusive deployment contract with that startup named MobileStar.
So the next time you walk into a Starbucks and see everyone hunched over their phone or laptop, you know who to credit (or blame) ;-)
Not only was Ken a senior vice president at EDS, but he was larger than life: big, powerful, and a hard driver. He managed a large business unit and I hoped to persuade him to adopt a then-new technology from my employer, IBM. The new technology was known by the acronym PROFS. But one of the many lessons I learned in developing this new business was this: don’t try to sell something to someone else that your team could use, but hasn’t. Customers don’t like to be guinea pigs.
IBM had developed a suite of office tools they named the Professional Office System, or PROFS. Because this was in the early 1980s, PCs were in their infancy and the Internet had yet to be fully developed (Al Gore was still working on it). So IBM launched this product to help people communicate and collaborate. It ran on IBM’s mainframes and people used “dumb terminals” to access the functionality.
At that time, IBM “consumed” fully 10% of the products it manufactured and savvy customers like EDS who knew this were always interested in how IBM used its own products. So when I assembled the team of IBM experts to show Ken and his staff this great new system, Ken quite rightly asked, “What’s IBM’s experience with this like?”
Ken looked straight at the IBM product manager when he asked the question and that product manager squirmed. He looked at the ground and then back at Ken, “Well, actually, we haven’t implemented it yet in the firm. But we plan to.”
Ken stood up, motioned for his staff to do the same, and said to the product manager: “Well, after you’ve used your own product and can tell me the real benefits based on your experience, I’ll be ready to listen.” And then they walked out of the room.
IBM did implement PROFS. I returned to Ken and sold him a PROFS system. But here’s the lesson: some customers are content to be early adopters (guinea pigs) and others are not. It’s important to know which one they are.

What impact does a product’s cost have on its market adoption? In the private sector, the answer is “a lot.” Conventional wisdom says that given the same level of delivered functionality, the lower cost an item is, the more likely customers are to purchase it.
In the defense sector, cost is sometimes seen as an “independent variable.” Since the objective of most military operations is to obtain or maintain dominance over an adversary, the unit cost of an item may not be the final determinant of whether to procure it. Often, saving the lives of friendly forces (‘survivability and lethality”) is frequently more important than unit cost concerns.
Yet when all of the costs of defense programs are “rolled up,” there is a ceiling and a budget approved by Congress. Seen through that lens then, affordability becomes highly relevant.
CommerceBasix’s team was awarded a contract to develop a design for an affordable soldier radio, a radio that could be fielded to every active duty soldier in the US ground forces, a radio that would have a unit cost of $1,000 instead of the Army approved but ultimately unaffordable radio that cost $37,000 each. If Congress could have been persuaded to actually purchase 500,000 units of the approved radio, it would cost nearly $20 billion. CommerceBasix demonstrated that adequate communications functionality could be achieved at a cost of $1,000 per radio by using a design based on “commercial off the shelf” (COTS) technology. And in so doing, the firm showed Army leadership how it could equip every solider with a radio for a total cost of 5% of the current budget. Here’s how we did this . . .
CommerceBasix used a proprietary analytical method it calls the Accelerated Army Modernization Process (AAMP).
By law, all weapons systems requirements must be defined by an Army command known as the Training and Doctrine Command (TRADOC). CommerceBasix worked with TRADOC to obtain a use case for a dismounted soldier radio that would be fielded to every member of a squad. Then, the firm retained a Swedish modeling and simulation company to model the use case in a multiple scenarios. Another firm was retained to perform signal propagation studies in urban environments (the most complex for radio communications). Subject matter experts in designing System on a Chip devices with embedded encryption were brought on to the team. Other subject matter experts experienced in developing commercial Mobile Ad Hoc Networks (MANET) contributed to the effort. Finally, a team of a dozen commercial cellular telephony designers from Bangalore were enlisted to develop a notional design with a complete bill of materials.
The resulting 300 page presentation, detailed design, and industry vetted bill of materials were presented to senior Army leadership. This “red team” design effort catalyzed seven additional research projects to validate CommerceBasix’s findings. The result was the creation of a new radio, the Rifleman Radio, which replaced the previous design. The Rifleman Radio, now in production, costs $2,800 each and has replaced the $37,000 radio originally approved. If the Army fields the original number of radios it planned, the Rifleman Radio will save the Army over $16 billion.
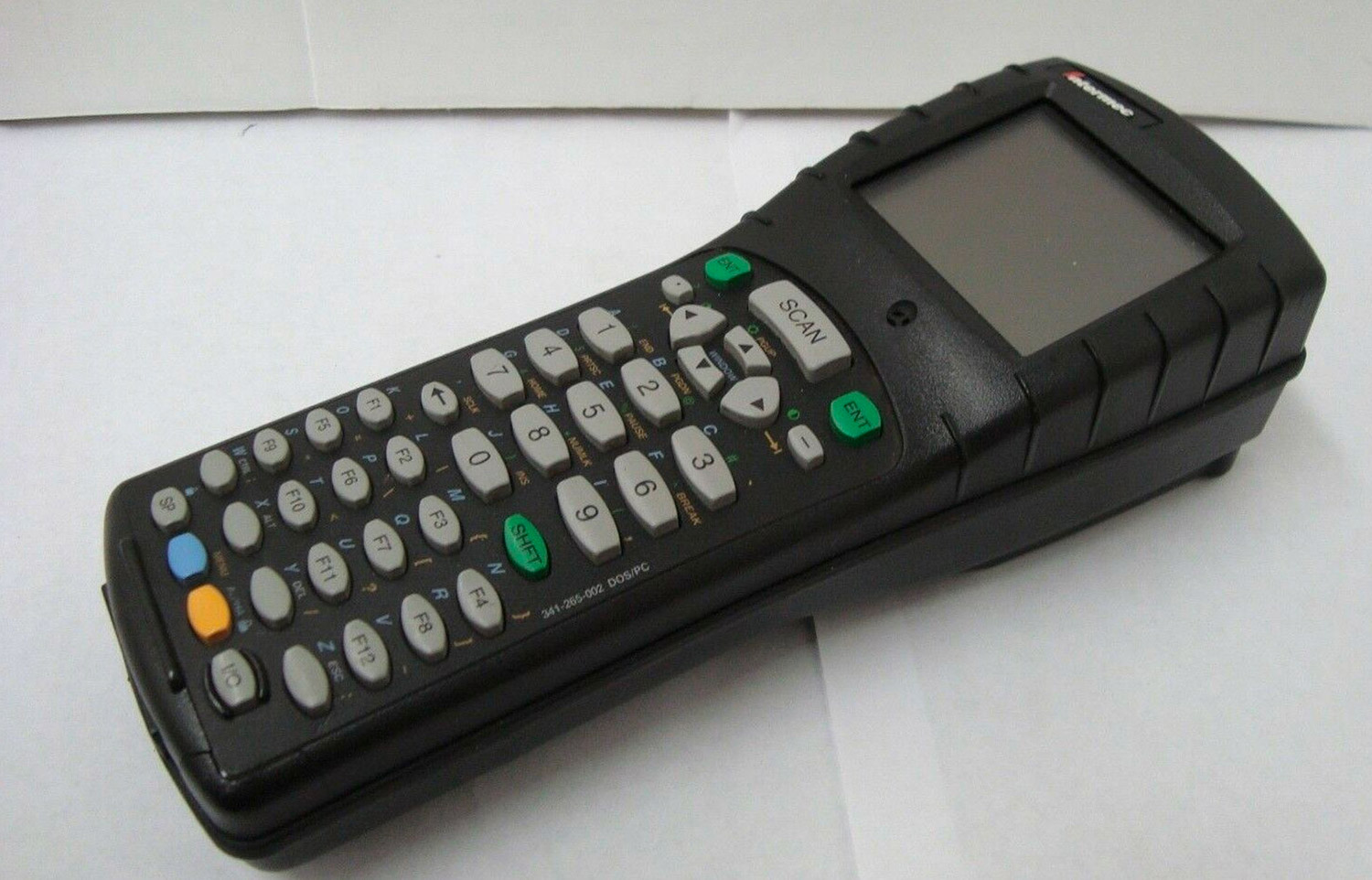
Our client, Norand Corporation (now a wholly owned subsidiary of Intermec had been developing handheld computers for years and in the process developed a robust patent portfolio. These patents included not just innovations relating to their core product family, handheld computers, but to networking technology operating in the unlicensed bands around 2.4 Ghz (now a part of the Wi-Fi bands).
But Norand faced some challenges relating to product costs and “time to market.” Each handheld computer includes a display, one of the most expensive components in the Bill of Materials (BOM). And because Norand wasn’t a high volume display customer compared to other vendors (e.g. Compaq), vendors did’t give them priority access to the latest display technology.
The challenge: find a way to reduce Norand’s display costs andget priority access to the latest display technology. Here’s how Mark did this . . .
First, Mark reviewed the list of display vendors Norand could purchase from. All were located in Japan and Korea. Second, Mark reviewed the business strategy of each to look for gaps in these firms’ IP portfolio that Norand might be able to fill with their patents. And he found four firms: three in Korea and one in Japan.
Mark then opened discussions with the US-based operations of each firm and offered this proposition: his client, Norand, was willing to license use of its RF patents in return for both early access to displays but also pricing that matched that of higher volume customers such as Compaq.
IP negotiations daily around the world. Strong IP portfolios can be used to block a competitor from a market, generate revenue through licensing, or offered in trade to reduce a demand to pay a license for use of another party’s IP.
But in this case, Norand’s IP was being offered as an asset in return for pricing and scheduling consideration. And it worked. The large Japanese manufacturer provided the best offer in response to the value proposition and a deal was struck.
The impact of this trade was significant. The reduction in cost translated into meaningfully higher margins for the products. Two years after the completion of the deal, Norand was purchased. As the CFO stated to Mark, “That deal alone helped us increase the sales price of the firm by $37M.”

The US military ground forces are equipped with a wide variety of electronic devices, some of which are worn or attached to the warfighter's body armor and others which are carried as part of a separate communications or weapons system. Because many of these devices need to communicate with each other, there is a need for a personal area network (PAN) that can connect these devices. The big question is this: should that network be a wired network or a wireless network?
CommerceBasix was hired to explore the feasibility of using a commercially available low power, wearable network to connect these devices. Several commercial-off-the-shelf (COTS) products were identified and tests performed by a former NSA RF engineer verified that the signal propagation of the body worn network was sufficiently low to fall within the Low Probability of Intercept (LPI) and Low Probability of Detection (LPD) thresholds.
But what would NSA think?
However, NSA did not like that there was ANY RF being used for connections. So, CommerceBasix performed a risk assessment of the data being communicated (short lived, tactical, squad level information) that had a an "information half life" of less than 5 minutes. The NSA wanted this RF traffic to be protected with a Type 1 security device, which if used, would have limited the use of the system to only those uniformed soldiers with a Secret clearance, about 3% of the fighting force. CommerceBasix countered that a) AES 256 would provide sufficient protection against a brute force attack by an OPFOR cryptanalyst and system (the work factor would be well above a five minute threshold) and b) the classification of the squad level data being communicated did not rise to the level requiring Type 1 protection.
An agreement was reached between the Army and NSA to keep the classification of this type of squad level communications below Type 1, obviating the need for a security clearance for this kind of network communications. The Army continues to explore the use of a wireless PAN as a means of connecting the many electronic devices used by the dismounted soldier.